A cybersecurity firm reported yesterday that a group of notorious hackers from North Korea managed to steal $3 billion worth of cryptocurrency from users by creating a fake blockchain game. Kaspersky Lab said that the Lazarus Group took advantage of a critical vulnerability in the Google Chrome browser that allowed them to extract the crypto wallets of their victims.
Lazarus Group: $3 Billion Crypto Heist
North Korean hackers were reported to have used the fake game to steal more than $3 billion – an operation the group successfully ran over a six-year period, from 2016 to 2022.
The heist is a negative result of Google’s failure to patch a vulnerability in the Chrome browser.
Meanwhile, a blockchain investigator conducting a separate investigation discovered that the Lazarus Group had executed 25 hacking attacks, and received 200 million crypto coins.
It also revealed the existence of a network of developers in North Korea working on “suspended” cryptocurrency projects. The network is said to receive a monthly payment of $500,000.
Questionable Game System
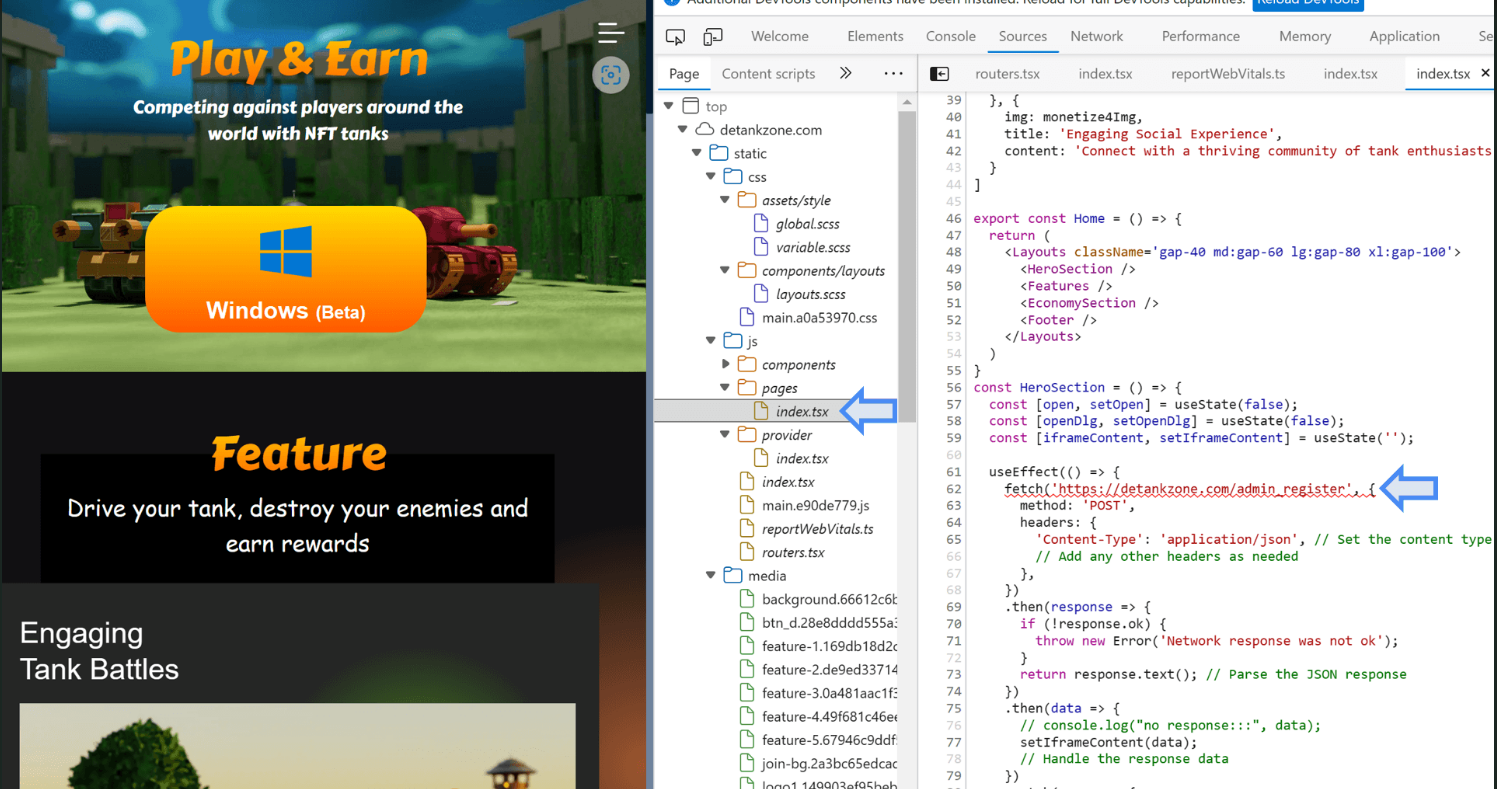
Vasily Berdnikov and Boris Larin, Kaspersky Labs analysts, said that the Lazarus Group created a fake game called DeTankZone or DeTankWar that revolves around Non-Fungible Tokens (NFTs) to empty the crypto wallets of their victims .
Analysts pointed out that the hackers exploited a zero-day vulnerability in the Chrome browser in their unscrupulous act.
Website appearance and the hidden exploit loader. Source: Kaspersky Lab
Berdnikov and Larin explained that the hackers used a fake game to lure their victims and lead them to a malicious website, which installed a malware called Manuscript.
Using Manuscript, hackers were able to corrupt Chrome’s memory, allowing them to obtain user passwords, authentication tokens, and everything else they needed to steal the crypto of their unwitting victims.
12 Days to Solve the Problem
Kaspersky Lab analysts discovered what Lazarus Group was doing in May. Berdnikov and Larin immediately escalated the issue to Google so the platform could fix the vulnerability.
However, Google was not ready to deal with the zero-day vulnerability, it took them 12 days to fix the vulnerability.
Boris Larin, chief security expert at Kaspersky Lab, said that the significant effort invested by the hacker group in the said hacking campaign shows that the group has an ambitious plan.
Larin noted that what the group did could have a wider impact than previously thought.
The Lazarus Group is a reminder that the war against hackers continues. The Chrome vulnerability emphasized that platforms should always ensure their security measures are updated and be aware of cybersecurity threats.
Featured image from Le Parisien, chart from TradingView
Source link